Cybersecurity breaches aren’t just for large businesses. No business is too small to be hacked. Over 70% of reported breaches actually affected businesses with 100 employees or less. You might be surprised to learn that represents over 90% of Rhode Island manufacturers! Your business must have a plan in place to help avoid the catastrophic impact of a cyber attack.
 Yes, cyber attacks can happen right here in Rhode Island. In fact, it just did. In January/February 2018, Chinese hackers breached a company that contracts with the Naval Undersea Warfare Center in Newport and stole sensitive data including some related to the development of a supersonic anti-ship missile designed for U.S. submarines.
Yes, cyber attacks can happen right here in Rhode Island. In fact, it just did. In January/February 2018, Chinese hackers breached a company that contracts with the Naval Undersea Warfare Center in Newport and stole sensitive data including some related to the development of a supersonic anti-ship missile designed for U.S. submarines.
Hackers are getting better and better at gaining access to sensitive information. A government subcontractor is an ideal place for them to start. And if they get into your systems, it could result in the end of operations, a loss of assets, and all of your employees out of work. Have you mitigated your business risks by protecting your information and developing an incident response plan?
Attacks can happen in a variety of ways. Among the most common for businesses are spear phishing and ransomware. Spear phishing targets specific individuals in a business to compromise information or funds. Ransomware, a type of malware, prohibits victims from accessing their own data. Hackers then demand payment (i.e., ransom) to decrypt and return access. Businesses can spend thousands of dollars trying to recover their own information
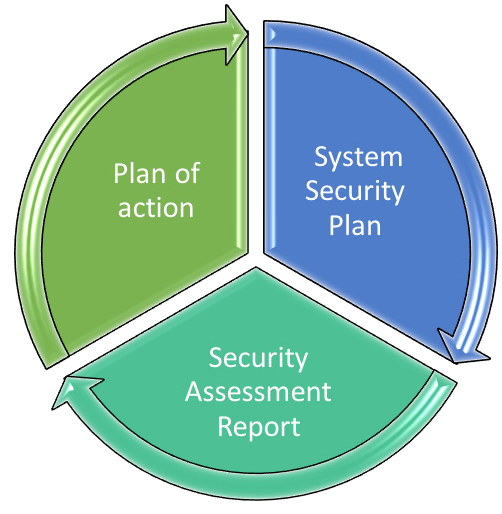
Is your information protected? When your customer asks for your System Security Plan and Plan of Action, how will you respond?
 Manufacturers in federal supply chains, whether primes or lower tiered subcontractors, are required to safeguard unclassified information. For federal contractors and subcontractors that process, store, or transmit federal contract information, there are basic safeguarding information requirements in place under FAR 52.204-21. However, it is anticipated that the GSA will soon adopt the broader requirements currently promulgated in the DFARS cybersecurity clause (252.204-7012) for all federal contracts.
Manufacturers in federal supply chains, whether primes or lower tiered subcontractors, are required to safeguard unclassified information. For federal contractors and subcontractors that process, store, or transmit federal contract information, there are basic safeguarding information requirements in place under FAR 52.204-21. However, it is anticipated that the GSA will soon adopt the broader requirements currently promulgated in the DFARS cybersecurity clause (252.204-7012) for all federal contracts.
This clause requires contractors and subcontractors to safeguard covered defense information and report cyber incidents. To protect information against events like cyber attacks, manufacturers handling covered defense information, such as technical drawings and specifications, or are considered to provide operationally critical support should have complied with Clause 252.204-7012 by implementing NIST SP 800-171 information security requirements by December 31, 2017.
The deadline has passed and your contracts may be at risk. DoD Contracting Officers and Primes are asking their contractors and subcontractors about, and for, their System Security Plans and Plans of Action. Is your company prepared? If your next solicitation requires that your proposal include your System Security Plan, will you be able to meet the requirement?
Even if your company is not part of the DoD supply chain, you should expect questions from your customers about how you are protecting their information. How will you respond?
Is your company compliant? Wading through the requirements (NIST SP 800-171) is daunting, but Polaris MEP is here to help.
Achieving Compliance
Achieving compliance is a straightforward process: develop a System Security Plan and Assessment Report and create your Plan of Action. Then begin to implement your plan.
Polaris MEP can help you
- complete an assessment of your current status;
- develop a system security plan and plan of action,
- connect with the resources to implement your plans of action, and
- document the policies and plans that are relevant to many of the requirements.
Don’t let your business fall victim to a cybersecurity breach. The deadline for compliance was December 31, 2017—every day you wait to protect your company puts your business and employees at risk!
Email Program Manager Kayla Viveiros for more information or check out our cybersecurity resources on this website. We’re here to help keep Rhode Island manufacturers on track and ready for success.
